The KEY WATCHER system uses key rings with built-in "Smart IC Chip" rather than just storing keys, and can only use designated keys with authorized cards and passwords, and can be monitored and controlled on key use and return times, user-connected operating PCs.
Patrol management system The composition| Installation of the operating program | - |
|---|---|
| Enter chips and patrol points | -You can configure more than 5,000 patrol points |
| Patrol Point Chip Attachment | -Attach the chip with the code entered as a program to the patrol post and patrol point. |
| Contact the chip at the patrol point | -After patrolling and inspecting the point, contact the information collector with the chip at the patrol point (in/out check, vehicle check, off state, others) |
| Access to information transmitter |
-Collect information collectors input with the patrol vehicle's activity situation, and access to information transmitters connected to computers. - The information transmitter decodes the data entered in the information collector and sends it to the computer. |
| Patrol and inspection details registration | -Establish a database by transmitting patrol activity data of an information collector to the computer through an information transmitter with an operation program built into the computer. |
The outer intrusion detection system is a device that installs a cable on an outer fence to receive information sensed on the cable through a controller and outputs it through an operation program. The system is configured to simultaneously detect tension and vibration in order to minimize the false alarm rate.
Applied location2. External security of corporate research institutes.
3. Detection of intrusion into a large factory.
2. A relay device that connects controller data cables and multi-cables, receives information sensed by multi-cables, and outputs signals to operating PCs and other devices.
3. It is a system that simultaneously adopts the advantages of an electronic Taut Wire with a very low multi-sensor cable malfunction rate and a precise vibration system with excellent sensing, and exhibits excellent intrusion detection capability.
This system promotes security and convenience for hotel guests when using various room amenities, and allows hotel managers to manage hotel rooms and facilities more efficiently and conveniently.
Cards will be issued and managed to guests and employees through central devices, and the system will be established to check and settle usage details when using convenience facilities such as restaurants, bars, and saunas as well as access to rooms using issued cards. In addition, each device is designed to suit the dignity of a luxury hotel, which can have a great effect on enhancing the image of the hotel as well as systematic convenience.
2. Card encoder: Information injection and issuance of smart and magnetic cards
3. Portable programmer: Employees can check and download information about the room.
4. Smart card lock: It is a lock for the room, and the issued card is inserted and opened.
5. Energy Saving Device: A device that controls power such as lighting, power, air conditioner, heater, etc. for a corresponding room.
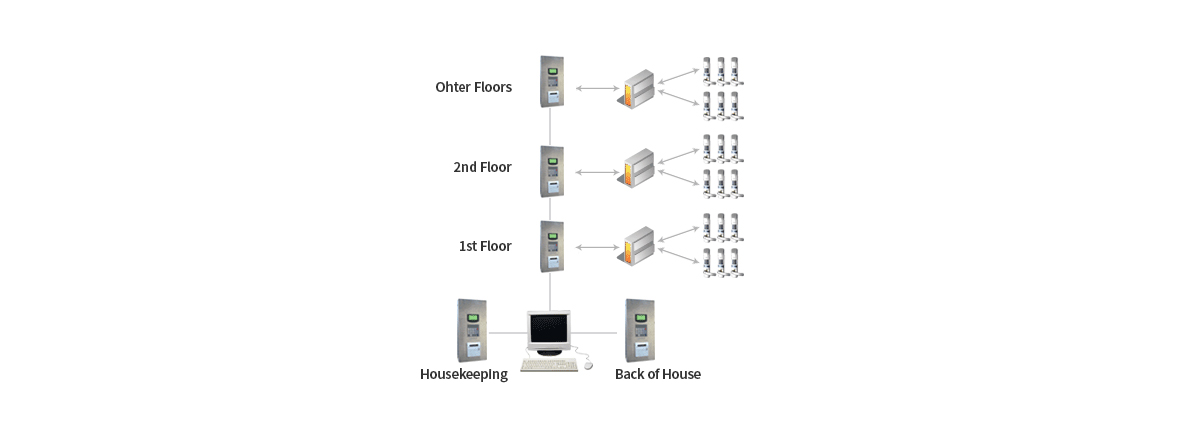
This system is a digital bus-type unmanned security system that can contribute to reducing security personnel, complete access control, crime prevention, and prevention of disaster prevention through cutting-edge digital exchange and video technology and various systems.
2. Safety has been further enhanced by strengthening safety and access control functions.
3. In the event of an abnormality within the generation, various call functions are concentrated in the security office (management office), so you can live with confidence.
4. You can feel a remarkable reduction in management labor costs.
5. Asset value is guaranteed compared to nearby apartments.